picoCTF 2019 - PcapPoisoning
picoCTF 2019 - PcapPoisoning
Write-up | picoCTF | PcapPoisoning
The link to the challenge is here
Description
How about some hide and seek heh? Download this file and find the flag.
Intial Analysis
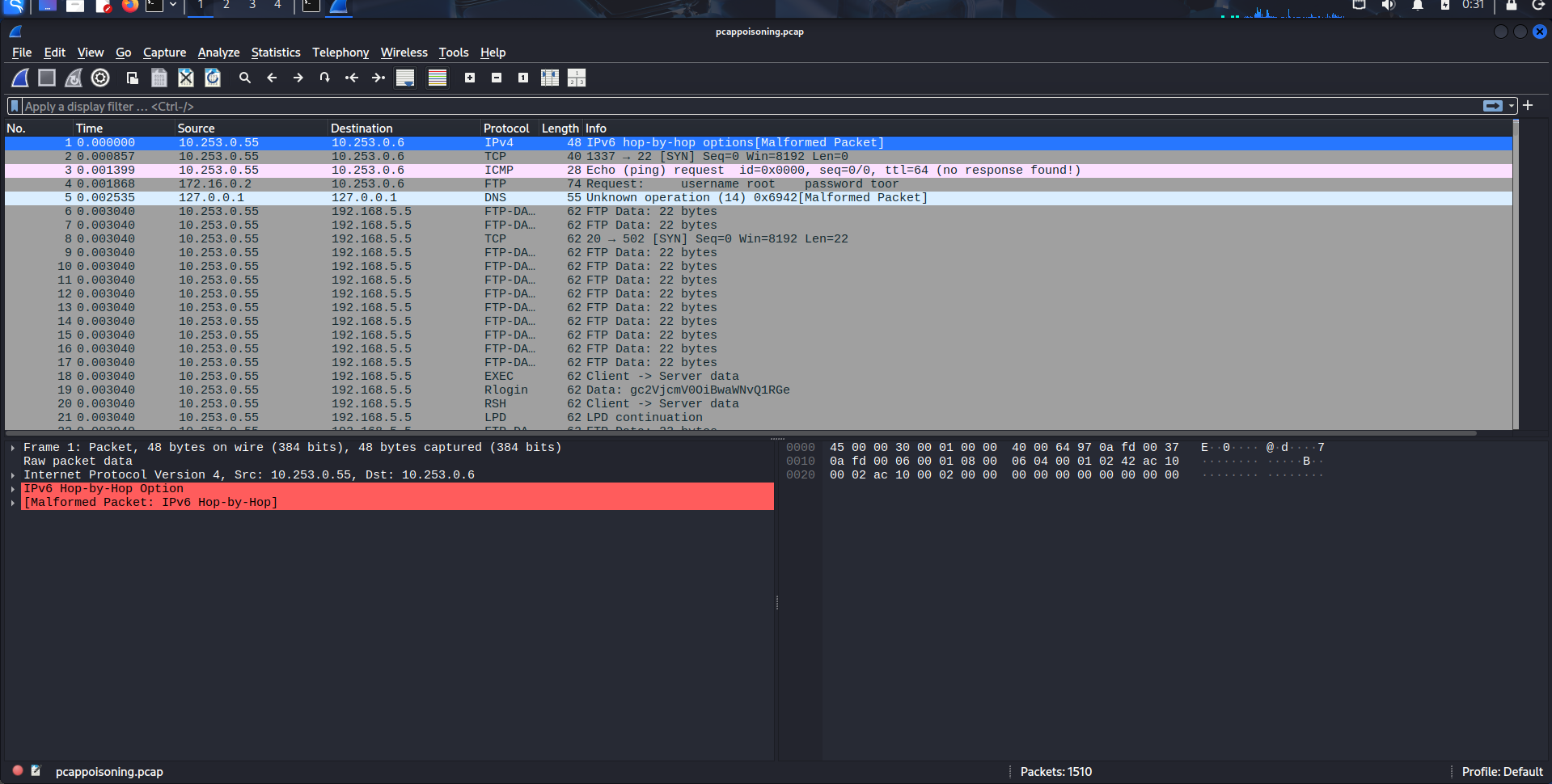
I got a file named trace.pcap. After file-ed the file, we can confirm it’s a real .pcap file. Now let’s begin.
Walkthrough
Notice that there’s FTP packet that contains the username and password: 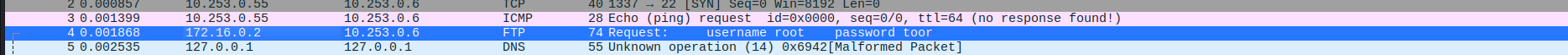
Follow the packet via Follow->TCP stream, the filter is changed to tcp.stream eq 1, and we can see there’s a TCP packet that appears: 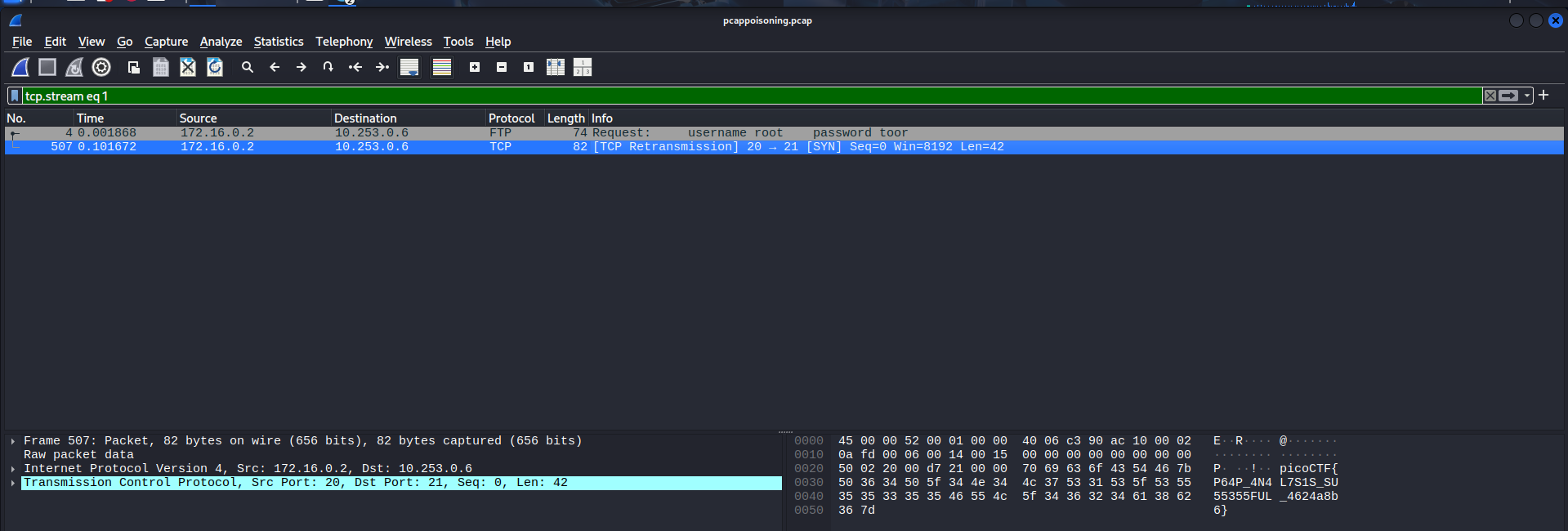
We can clearly see the flag is right there. Copy it as ASCII text and we got the flag.
The flag is (click the arrow below):
**picoCTF{P64P_4N4L7S1S_SU55355FUL_4624a8b6}**
This post is licensed under CC BY 4.0 by the author.